Scientific Research & Exploration: Look Into the Globe With Study and Technology
Quantum computer systems are coming. And when they appear, they are probably to topple the approach we protect delicate info.
Unlike timeless computer systems, quantum computer systems harness quantum mechanical results– like superposition and intricacy– to treatment and shop info in a kind past the 0s and 1 s that are electronic littles. These “quantum little bits”– or qubits — can open significant computer power.
” Like a number of effective contemporary innovations, you can make use of [quantum computing] for wonderful great,” Rebecca Krauthamer , a technical ethicist and chief executive officer of cybersecurity company QuSecure, informed Live Scientific research study.” And you can likewise use it for harmful features.”
When functional quantum computer system systems first come online, great deals of individuals– and also most big companies– will certainly still rely upon ageless computer system systems. Cryptographers therefore call for ahead up with ways to guard information from effective quantum computer systems, making use of programs that can operate a regular laptop computer.
That’s where the area of post-quantum cryptography can be found in. Various groups of researchers are contending to develop cryptographic formulas that can get away hacking by quantum computer systems before they are turned out. Numerous of these cryptographic formulas depend upon recently developed solutions, while others are changing to centuries-old ones. Yet all have something alike: They can not be comfortably split by solutions that work with a quantum computer system.
” It looks like a structure for a three-story framework, and afterwards we created a 100 -story skyscraper on it. “
Michele Mosca, creator and chief executive officer of cybersecurity firm evolutionQ
The frameworks of cryptography
Cryptography return centuries; the earliest comprehended circumstances is a cipher formed right into old Egyptian rock in 1900 B.C. Yet the cryptography utilized by the bulk of software application systems today trusts public important formulas. In these systems, the computer system uses formulas– which commonly include factoring the item of 2 significant prime numbers– to create both a public secret and a personal secret. The public trick is utilized to climb the information, while the individual trick, which is provided simply to the sender, can be utilized to unscramble the info.
To crack such cryptography, cyberpunks and different other transgressors typically must factor the products of big prime numbers or look for the individual method by toughness– basically throwing out hunches and seeing what sticks. This is a challenging trouble for ageless computer system systems because of the reality that they need to assess each inkling one after one more, which restricts simply exactly how promptly the variables can be recognized.

A 100 -tale skyscraper on a three-story structure
Nowadays, timeless computer system systems typically sew with each various other countless safety formulas, performed at different locations, such as a hard drive or the web.
“You can consider formulas like creating blocks,” Britta Hale , a computer system scientist at the Naval Postgraduate University, notified Live Scientific research (Hale was chatting purely in her capability as a specialist and out component of the institution or any type of kind of company.) When the blocks are piled, every one comprises a small item of the castle that avoids cyberpunks.
Yet most of this cryptographic centers was boosted a structure created in the 1990 s and very early 2000 s, when the internet was a lot less primary to our lives and quantum computer system systems were mainly presumed experiments. “It resembles a structure for a three-story framework, and after that we created a 100 -story skyscraper on it,” Michele Mosca , creator and chief executive officer of cybersecurity company evolutionQ, informed Live Scientific research. “And we’re type of hoping it’s alright.”
It might take a traditional computer system thousands and also billions of years to divide a genuinely difficult prime factorization formula, yet an efficient quantum computer system can typically settle the similar formula in a couple of hours. That’s since a quantum computer system can run several estimations at the exact same time by adjusting quantum superposition, in which qubits can exist in a number of states all at once. In 1994, American mathematician Peter Shor revealed that quantum computer systems can successfully run formulas that will quickly fix prime-number factoring problems. Subsequently, quantum computer system systems could, in theory, take apart the cryptographic citadels we presently use to shield our information.
Post-quantum cryptography means to alter obsolete structure with less-hackable blocks, product by product. And the very first step is to find the proper math problems to utilize. Often, that shows returning to solutions that have really been around for centuries.
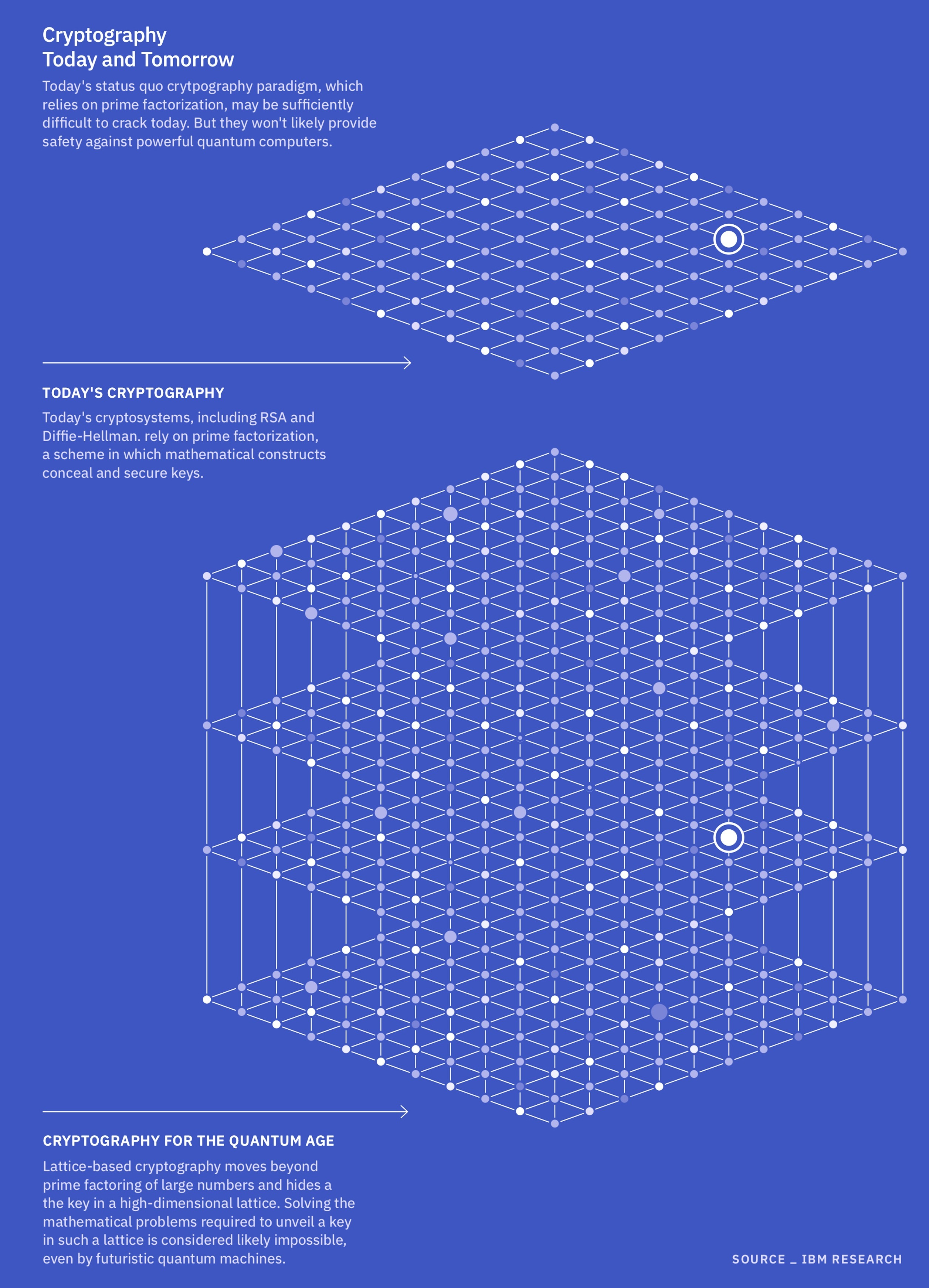
Currently, the National Institute of Demands and Innovation (NIST) is checking out 4 issues as feasible structures for post-quantum cryptography. 3 come from a mathematical relative called arranged latticeworks. These problems ask issues relating to the vectors– mathematical terms that specify guidelines and dimension in between interconnected nodes– like the link consider a spiderweb, Mosca claimed. These latticeworks can theoretically have a limitless selection of nodes and exist in several measurements.
Experts assume latticework problems will certainly be difficult for a quantum computer system to fracture because, unlike a few other cryptographic formulas, latticework problems do not rely upon factoring lots.
Rather, they make use of the vectors in between nodes to create a crucial and protect the information. Addressing these problems might involve, as an instance, calculating the fastest vector in the latticework, or trying to identify which vectors are closest per various other. If you have the trick– typically a “great” beginning vector– these problems might be rather straightforward. Yet without that method, they are devilishly tough. That is because of the reality that no person has actually created a formula, like Shor’s formula, that can successfully fix these problems utilizing quantum computer system design.
The fourth problem that NIST is thinking about comes from a group called hash features. Hash attributes feature by taking the electronic method for opening up a specific element on an information table, rushing that important and pushing it right into a much shorter code. This kind of formula is currently a keystone of contemporary cybersecurity, so in theory, it has to be added straightforward to update timeless computer systems to a quantum-proof variant compared to different other post-quantum cryptographic systems, Mosca asserted. And similarly to arranged latticeworks, they can not promptly be taken care of by strength alone; you call for some tip regarding what’s taking place inside the “black box” essential generator to figure them out within the age of deep area.
Yet these 4 problems do not cover every one of the potentially quantum-safe solutions around. As an example, the European Settlement is looking into an error-correcting code described as the McEliece cryptosystem. Created greater than 40 years back by American developer Robert McEliece, this system uses arbitrary number generation to create a public and individual trick, together with a documents security formula. The recipient of the exclusive important usages a set cipher to decrypt the info.
McEliece documents security is primarily thought about both quicker and added safe than one of the most often utilized public-key cryptosystem, called Rivest-Shamir-Adleman. Similar to a hash attribute, prospective cyberpunks require some understanding right into its black-box documents security to fix it. On the reward side, specialists consider this system truly safe ; on the drawback, likewise the secrets to unscramble the information must be fine-tuned making use of extremely significant, frustrating matrices, requiring a large amount of power to run.
A comparable error-correcting code, described as Hamming Quasi-Cyclic (HQC), was recently picked by NIST as a back-up to its main prospects. Its primary advantage over the typical McEliece system is that it uses smaller sized secret and ciphertext dimensions
Another type of formula that sometimes appears in conversations relating to post-quantum cryptography is the elliptic contour, Bharat Rawal , a computer system and info scientist at Capitol Modern modern technology College in Maryland, informed Live Scientific research study. These problems return a minimum of to old Greece. Elliptic contour cryptography uses basic algebra– figuring out the variables on a curved line– to protect secrets. Some professionals think a brand-new elliptic shape formula could avert hacking by a quantum computer system. However, others claim that a cyberpunk could hypothetically utilize Shor’s formula on a quantum computer system to harm most well-known elliptic contour formulas, making them a less-secure choice.
No silver bullet
In the race to discover quantum-safe cryptographic formulas, there will not be a silver bullet or a one-size-fits-all solution. For example, there’s regularly a concession in managing power; it would certainly not make much sensation to utilize center, power-hungry formulas to shield low-priority information when a simpler system could be flawlessly enough.
“It’s not like one formula [combination] will certainly be the approach to go; it depends on what they’re securing,” Hale claimed.
In Fact, it works for companies that make use of timeless computer system systems to have more than one formula that can shield their information from quantum threats. By doing this, “if one is verified to be vulnerable, you can comfortably switch to one that was disappointed prone,” Krauthamer claimed. Krauthamer’s team is currently working together with the united state Armed force to boost the company’s ability to faultlessly alter in between quantum-safe formulas– an attribute called cryptographic mastery.
Despite the fact that valuable (or “cryptographically proper”) quantum computer systems are still a variety of years away, it is important to start planning for them currently, professionals mentioned. “It can take a number of years to upgrade existing systems to be prepared for post-quantum cryptography,” Douglas Van Bossuyt , a systems designer at the Naval Postgraduate Establishment, notified Live Scientific research in an e-mail. (Van Bossuyt was chatting totally as a subject-matter expert and out component of the Naval Postgraduate Institution, the Navy or the Division of Security.) Some systems are difficult to upgrade from a coding point of view. And some, such as those aboard militaries craft, can be tough– or probably difficult– for scientists and developers to access literally.
Various other experts acknowledge that post-quantum cryptography is a pushing trouble. There’s similarly the opportunity that, once more, since quantum computer systems are so effective, we will not really recognize when a company gets access to such an efficient equipment,” Krauthamer asserted.
There’s furthermore the threat of “harvest-now, decrypt-later” attacks. Destructive stars can scoop up delicate encrypted info and wait up until they have accessibility to a quantum computer system that can damaging the safety. These sorts of assaults can have a vast array of targets, consisting of checking account, individual health information and nationwide safety data sources. The quicker we can shield such info from quantum computer system systems, the far better, Van Bossuyt mentioned.
And much like any type of type of cybersecurity strategy, post-quantum cryptography will certainly not stand for an end factor. The arms race in between cyberpunks and security experts will certainly continue to be to create well right into the future, in manner ins which we can just begin to anticipate. It might recommend producing safety formulas that work with a quantum computer system as opposed to a traditional one or situating ways to combat quantum expert system, Rawal asserted.
The world requires to maintain dealing with this since if these [post-quantum equations] are damaged, we do not desire to wait twenty years ahead up with the substitute,” Mosca mentioned.
Look into the complete write-up from the initial source
.